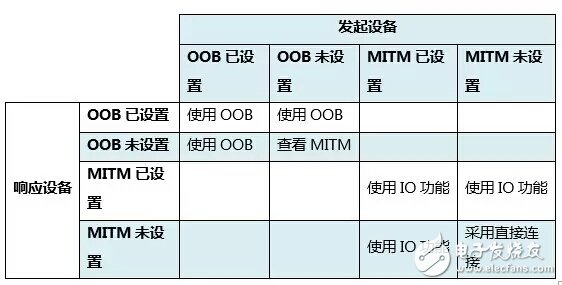
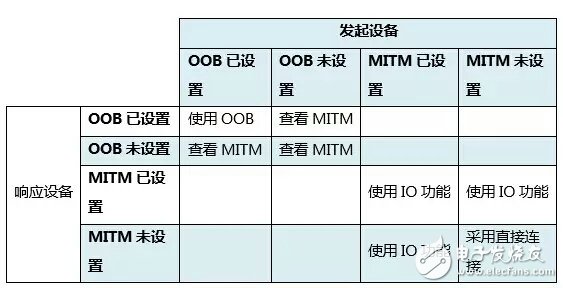
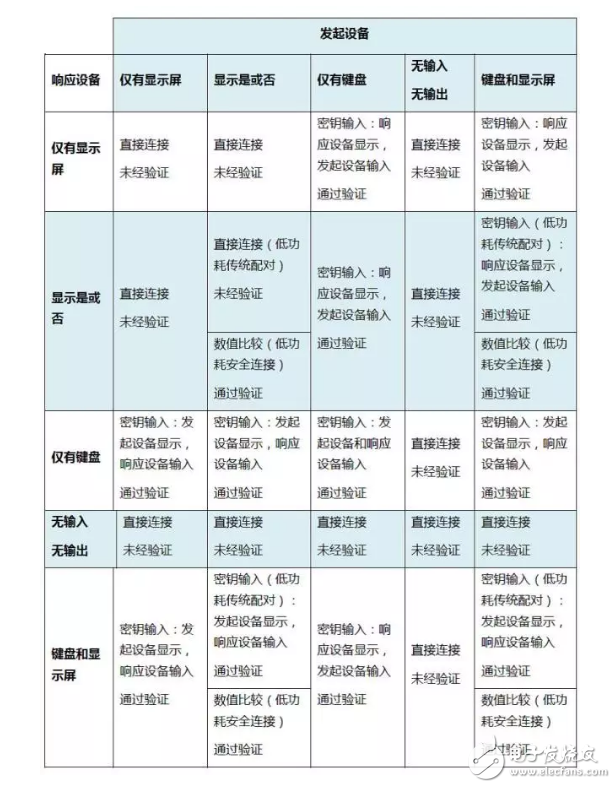
In "Bluetooth Pairing - Pairing Feature Exchange" , we talked about the Bluetooth pairing feature exchange of Low Energy (LE). The pairing feature exchange enables both the initiating device and the responding device of the connection to learn the pairing characteristics of each other. The pairing features that can be enabled are: OOB (Out-of-Band) data flag MITM (Man-in-the-Middle) flag SC—LE Secure ConnecTIon flag IO Cap-IO function After the feature exchange is completed, both devices can select the key generation method used in the next stage. The list below shows the key generation methods for low-power Legacy Pairing and LE Secure ConnecTIon. Low power traditional pairing: Direct connection (Just Works) Passkey Entry Out-of-Band (OOB) In addition to the above three methods, a low-power secure connection adds a new method: Numerical comparison (Numeric Comparison) Operation flow (Workflow) The following describes the key generation operation process of the selected device: Step 1: Check the secure connection bits in the pairing feature exchange framework. If both secure connection bits are equal to 1, then a low-power secure connection is used and step 2 is entered. Otherwise use low power traditional pairing and go to step 3. Step 2: When using a low-power secure connection, the initiating device and the responding device should follow the matrix selection pairing method as follows: "Using OOB" means selecting Out-of-Band "Viewing MITM" means ignoring "OOB" and viewing the MITM logo "Use IO function", go to step 4, select the key generation method according to the IO function of both devices Step 3: When using Low-Power Legacy Pairing, the initiating device and the responding device should follow the matrix selection pairing method as follows: "Using OOB" means selecting Out-of-Band "Viewing MITM" means ignoring "OOB" and viewing the MITM logo "Use IO function", go to step 4, select the key generation method according to the IO function of both devices Step 4: The following is a mapping of IO functions and key generation methods. According to the chart below, both the initiating device and the responding device can find a suitable connection method based on their pairing characteristics. The initiating device and the responding device can then learn how the key generation phase will be applied. In a follow-up third article, Xiaobian will continue to show how to generate a matching key in a low-power traditional pairing by using Keykey Entry. Charging Cable Bracelet,Charging Cable For Iphone,Charging Cable,Micro Usb Hebei Baisiwei Import&Export Trade Co., LTD. , https://www.baisiweicable.com